Mobile banking stopped being a side channel a long time ago. The market surpassed $1.3 billion in revenue last year and is projected to triple by 2030 with a CAGR of over 15%, while global users grew from 1.9 billion in 2020 to over 2.5 billion by June 2023, with projections of approximately 3 billion by 2025, according to SDK.finance’s mobile banking market overview.
That scale changes the engineering conversation. A banking app isn’t a polished account dashboard with a transfer button. It’s a regulated transaction surface, a security boundary, a customer trust test, and usually a thin modern shell wrapped around old banking infrastructure.
For teams building in React, the hardest decisions rarely sit in the UI layer. They sit in the trade-offs between React Native and Next.js PWA, in the seams between your frontend and legacy core systems, and in the boring but decisive implementation details like token storage, KYC retries, idempotent payments, and release gates. Banking mobile app development rewards teams that design for failure early. It punishes teams that assume a nice component library and a fast sprint cadence are enough.
The High-Stakes World of Modern Banking Apps
The opportunity in mobile banking is obvious. The risk is less obvious until you start building. In most consumer apps, a bug creates friction. In a banking app, a bug can lock a user out, duplicate a payment attempt, expose account data, or trigger a support incident that damages trust immediately.
That’s why banking mobile app development has a different bar from standard product work. Teams aren’t only shipping screens. They’re shipping a system that has to survive poor connectivity, delayed bank responses, provider outages, fraud controls, app store review cycles, and compliance review. The interface is the visible part. The product is the reliability behind it.
For React teams, that tension is useful. React Native gives you tighter access to device features and a more app-like feel. Next.js PWAs give you easier web distribution, shared frontend skills, and faster iteration for some use cases. Neither choice is universally right. The right answer depends on your authentication model, your offline expectations, your compliance posture, and how much native device capability your product needs.
Banking apps fail when teams treat them like generic SaaS dashboards with a payments tab.
A strong build starts with three assumptions.
- Your backend is never as clean as the prototype: Legacy systems, partner APIs, and internal services will disagree on payload shape, timing, and error behavior.
- Your users won't forgive ambiguity: “Pending,” “processing,” and “failed” need exact product definitions, not placeholder copy.
- Security decisions belong in architecture, not polish sprints: Secure storage, session handling, logging controls, and key management can't be bolted on later.
React-based teams can achieve excellent results. React is fast for product iteration. Next.js is strong for structured web flows and server-managed rendering. React Native is mature enough for serious financial products. But the stack only works if the architecture respects banking reality.
Deconstructing the App Blueprint and Feature Set
Most first banking app roadmaps are either too big or too shallow. Teams try to ship everything at once, or they call an app “MVP” when it only supports login and balance viewing. In practice, a useful banking product needs a clear split between table-stakes capabilities and differentiators.

The features every real banking app needs
These are the functions users assume will work on day one. If any of them feel incomplete, the whole app feels untrustworthy.
Minimum viable banking app: secure onboarding, account overview, transaction history, transfers, bill pay, alerts, card controls, and support access.
A serious baseline usually includes:
- Account overview: Checking, savings, credit, loan, and investment views often arrive from different systems. The UI should unify them without pretending the data freshness is identical across all account types.
- Transaction history: Users want searchable history, merchant labels, pending states, posted states, and useful descriptions. The hard part isn't the list UI. It's normalizing inconsistent transaction metadata from upstream systems.
- Transfers: Internal transfers are the easy case. External bank transfers, ACH, wires, and peer-to-peer flows add cutoff logic, status transitions, and stronger fraud controls.
- Bill payments: Scheduled payments, payee setup, confirmation states, and cancellation windows need careful product rules. The frontend should never hide processing uncertainty behind a fake “success” screen.
- Card management: Freeze card, unfreeze card, view masked card details, set travel notices where applicable, and surface suspicious activity alerts clearly.
- Notifications and alerts: Low balance, transfer updates, failed payments, password changes, new device sign-ins. Push notifications are only useful if they match real backend state.
What users expect versus what engineers inherit
The user thinks “show my accounts.” The system often means “aggregate data from a core ledger, a card processor, a loan platform, and a reporting cache, then resolve timing differences.”
The user thinks “send money.” The system means validating available balance, checking limits, screening fraud patterns, creating an idempotent instruction, calling a processor, waiting for callback confirmation, and reconciling the final state if a webhook arrives late.
That mismatch is where many teams burn time. Product defines a simple experience. Engineering inherits distributed complexity.
Value-add features that actually matter
Differentiators should come after the basics are stable. The mistake is adding flashy features before fixing the core transaction surface.
Useful second-wave features include:
- Personal finance management: Categorization, spending views, cash-flow summaries, and savings nudges can help users stay in the app instead of treating it as a utility.
- AI-driven insights: These work when they explain something specific, like recurring charges or unusual spending patterns. They fail when they produce vague tips that read like generic marketing copy.
- Chat and support workflows: A bot can help route intent, but banking support still needs clean escalation to a human for disputes, payment reversals, identity checks, and locked-account events.
- Biometric login: This is now expected in high-quality banking apps, but it should initiate a secure session. It should not become a shortcut around proper token handling.
- Document center and statements: Boring feature, high practical value. Users need fast access to statements, notices, and tax-related documents without hunting through a web portal.
MVP priorities that keep teams honest
If you’re planning an initial release, cut by risk, not by visual appeal.
A pragmatic order looks like this:
- Onboarding and authentication
- Read-only account and transaction views
- Transfers and bill pay
- Card controls and alerts
- Support, disputes, and document access
- PFM and AI enhancements
That ordering works because it aligns engineering effort with trust. A budgeting chart can wait. A broken transfer flow can't.
Choosing Your Architecture and React-Based Stack
The frontend decision gets the most debate, but the system boundary matters more. In banking mobile app development, the app usually sits on top of old core banking systems, vendor APIs, and internal services that weren't designed for modern client apps.

Legacy integration is the real architecture problem
Many banks still run on infrastructure that can't support modern real-time expectations cleanly. That’s not a niche complaint. MindInventory’s banking app development analysis says 68% of fintech teams struggle with legacy interoperability when adopting React Native or PWA-based banking UIs, and agencies report 40% project delays from unresolved core banking silos.
If you connect your React client directly to a patchwork of internal APIs, you create three problems fast:
- client code absorbs backend inconsistency
- security logic spreads across too many surfaces
- versioning becomes brittle when one legacy system changes behavior
The fix is usually a Backend for Frontend, or BFF.
Why a BFF works well in banking
A BFF gives your React Native app or Next.js frontend a controlled contract. It shapes payloads, centralizes authorization checks, translates legacy fields, and hides vendor-specific weirdness from the UI. It also lets you add app-specific orchestration without changing core systems every sprint.
A good banking BFF usually handles:
- Response normalization: one account summary schema, even if upstream systems disagree
- Session-aware policy checks: device state, step-up auth triggers, feature flags
- Aggregation logic: balances, cards, statements, transfer status, support context
- Observability hooks: request tracing, redaction-safe logs, provider latency tracking
Without it, the frontend becomes the adapter layer. That’s a costly mistake.
Practical rule: keep React focused on presentation, local interaction state, and well-defined workflows. Keep orchestration and policy enforcement in the BFF.
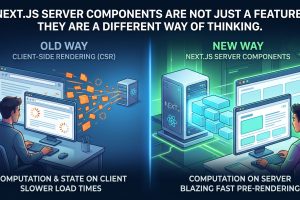
React Native versus Next.js PWA
This is the decision many teams want answered with a slogan. There isn’t one. Use criteria.
| Criterion | React Native | Next.js PWA |
|---|---|---|
| Distribution model | App store deployment with native packaging | Browser-first delivery with installable web app support |
| Biometrics access | Strong fit for Face ID, Touch ID, fingerprint modules, and device APIs | Possible through web standards like WebAuthn, but browser support and UX vary |
| Offline behavior | Better control for secure local workflows and queued actions | Good for cached read flows, weaker for complex secure offline interactions |
| Performance feel | Closer to native app expectations for gesture-heavy and device-integrated UX | Fast for content and dashboard flows, depends heavily on network and browser conditions |
| Update speed | App releases require mobile delivery workflow and store review considerations | Web deployments are faster and simpler to ship |
| Security posture | Better access to platform secure storage like Keychain and Keystore | Strong server-managed patterns possible, but client storage choices need more restraint |
| Use case fit | Best for primary banking apps with rich device integration | Best for companion experiences, onboarding portals, account access, and lower-friction distribution |
When React Native is the better choice
Choose React Native when the banking app is the main product surface, not just an access channel. It’s usually the stronger choice when you need native biometrics, deeper device integration, predictable mobile UX, and stronger control over secure client storage.
It also works better when users expect a “real bank app” experience. That includes faster login flows, camera-based document capture, smoother sensitive-action confirmations, and a more contained environment for session handling.
When Next.js PWA is the better choice
Choose Next.js PWA when distribution speed matters more than native feel, or when your product leans heavily on web onboarding, account access, informational dashboards, or customer acquisition flows.
A PWA can also be a smart first move for a bank launching a digital experience before committing to full native investment. If the most important workflows are identity capture, product application, dashboard viewing, and support access, Next.js can move quickly. This is especially true when your team already has strong SSR, routing, and full-stack JavaScript capability. For teams comparing broader implementation patterns in financial products, this fintech app development guide for React and Next.js teams is a useful companion.
The stack choices that age well
Within the React ecosystem, the combinations that usually hold up are straightforward:
- React Native app plus Node-based BFF: good for mobile-first banking with native auth and vendor orchestration
- Next.js app router plus server actions or API routes plus BFF: good for secure web delivery and structured onboarding
- TanStack Query or SWR for server state: both help, but only when query invalidation and cache boundaries are designed carefully
- TypeScript everywhere: especially important for payment, identity, and ledger-adjacent flows
The wrong architecture in banking doesn't merely slow feature delivery. It turns every provider integration into custom repair work.
Integrating Secure Authentication KYC and Payments
Most banking apps feel easy when you click through a polished prototype. The hard part starts when a real user signs up from a spotty mobile network, fails document capture twice, links an account through an aggregator, and retries a payment after a timeout. That entire path needs to behave predictably.

Authentication should be layered, not clever
For most products, the safest default is an OAuth 2.0 or OIDC-based model managed through your backend. The client starts an auth flow, the identity layer completes verification, and the app receives only what it needs for session continuity. Don’t let the mobile client become the source of truth for authorization.
For React Native, biometric login usually wraps secure token retrieval from native storage and then re-establishes a valid session. For a Next.js PWA, WebAuthn can provide strong browser-based authentication, but the exact device and browser matrix matters. Teams often overestimate how “native” biometric UX will feel on the web across different environments.
The implementation mistakes I see most often are simple:
- Storing sensitive tokens in the wrong place: avoid generic client storage for anything that can extend or recreate a privileged session.
- Confusing biometric access with authentication: biometrics should access a secure secret or authorize a local step. They don’t replace your auth model.
- Skipping device-change handling: new device enrollment, revoked sessions, and suspicious sign-in recovery need explicit product flows.
KYC is a user journey with failure branches
KYC and AML integrations look straightforward in vendor demos. Real users introduce glare, damaged documents, mismatched names, stale addresses, and partial session abandonment.
A practical flow usually looks like this:
- Collect baseline identity information
- Capture document images or live verification assets
- Send data to the verification provider
- Handle pending, approved, and manual-review outcomes
- Resume onboarding without losing state
The key engineering point is resumability. Users drop out. Providers time out. Reviews go asynchronous. If your onboarding flow assumes everything completes in one pass, support tickets pile up fast.
Build KYC like a long-running workflow, not a single API call.
That means preserving progress, surfacing exact status, and making retries targeted. If the selfie fails, retry the selfie step. Don’t reset the whole application. If address verification is pending, don’t show a generic loading screen with no next action.
It also means your React frontend should treat KYC provider responses as external states, not UI states. “Needs review,” “additional document required,” and “verification expired” deserve first-class modeling in your app.
Payments fail in ways demos don't show
A user links funding, initiates a payment, sees a spinner, loses signal, retries, and now support has to answer the worst question in finance UI: “Did I pay twice?”
That’s why payment integrations live or die on idempotency, state reconciliation, and webhook discipline.
Use API-driven providers for cards, transfers, or ACH where that fits your product, but never let the frontend decide final payment truth. The client can initiate intent. The backend owns authoritative status.
Common gotchas:
- Webhook trust: verify signatures, reject malformed events, and process events idempotently.
- Async settlement confusion: “submitted” is not the same as “completed.”
- Timeout ambiguity: if the processor doesn’t answer in time, the app must show a recoverable pending state, not false success or false failure.
- Retry hazards: retries should reuse idempotency controls so a user can safely tap again without duplicating movement.
For teams implementing provider-side transaction flows in JavaScript stacks, this payment gateway development walkthrough for React and Next.js projects is a useful technical reference.
A short explainer is useful here before the next point:
Integration contracts matter more than SDK convenience
SDKs help with speed, but they can hide behavior. Before adopting one, answer these questions:
- Who owns retries, the SDK or your backend?
- Can you audit request and event flow cleanly?
- How are error objects structured?
- Can you simulate pending and failure conditions in test environments?
- What happens if the provider is partially degraded, not fully down?
Those questions matter because banking mobile app development depends on confidence at the edges. KYC and payments are edge-heavy systems. If your app can’t explain the current state clearly, users assume the worst.
Hardening Your App with Encryption and Compliance
Security work in banking apps shouldn't read like a wishlist. It belongs in the baseline architecture, sprint planning, code review, and release criteria. If a team treats encryption and compliance as late-stage polish, they usually end up rewriting core flows.

Protect data in transit
Every banking app should enforce modern transport security across every network boundary. That includes app-to-BFF traffic, BFF-to-internal-service traffic, and BFF-to-provider traffic. One weak internal integration can become the weakest link in the system.
For mobile apps, certificate pinning can be appropriate in higher-assurance environments, but it has operational cost. Rotations, staging parity, and failure handling need planning. Teams sometimes add pinning for optics and then weaken it later because release operations become painful.
A better approach is deliberate hardening:
- Enforce TLS consistently: no mixed standards across internal and external calls.
- Reduce trust surface: only allow known endpoints and clearly owned integrations.
- Log safely: never leak secrets, raw identity documents, or full financial payloads into traces.
Protect data at rest on the device
At this point, React teams can make very good or very bad choices.
For React Native, sensitive material belongs in platform-backed secure storage such as iOS Keychain and Android Keystore. For Next.js PWAs, be extremely careful about what is stored client-side at all. A lot of web security posture improves when you keep sensitive session handling server-managed and avoid persisting privileged tokens in browser-accessible storage.
What doesn't work well is convenience-driven storage.
- Don't put secrets in generic local storage layers
- Don't cache sensitive account payloads without strict need
- Don't leave debug logging enabled around auth and payment flows
Client devices are hostile environments from a security perspective. Treat them that way.
Encryption is only part of the story
Teams often say “we encrypt everything,” then ignore surrounding controls. A secure banking app also needs:
| Area | What strong implementation looks like |
|---|---|
| Session management | short-lived sessions, re-auth on sensitive actions, clean revocation paths |
| Authorization | least-privilege checks on every protected backend action |
| Secrets handling | environment isolation, managed secret storage, strict rotation process |
| Auditability | immutable event trails for security-sensitive operations |
| Fraud-aware UX | visible alerts for device changes, password resets, and unusual payment attempts |
Security is strongest when product, backend, and mobile teams agree on exact behavior for risky actions before coding starts.
Compliance changes architecture
Compliance is often discussed as paperwork. In implementation, it changes data flow, retention, and access patterns.
A few recurring examples:
- PCI DSS: if card data enters your environment, your scope and controls tighten fast. Use tokenization and hosted fields or provider-controlled collection where possible.
- GDPR: data minimization, retention controls, deletion workflows, and consent records need technical support, not just legal language.
- PSD2 principles and open banking expectations: strong customer authentication and consent handling affect the user journey and API design.
These frameworks push teams toward cleaner boundaries. They reward systems that separate concerns well. A BFF, strict service ownership, and explicit data classification make compliance easier. Sloppy client-side persistence and broad internal access make it harder.
Security backlog items that shouldn't slip
A useful backlog for banking mobile app development usually includes these essential items early:
- Threat modeling sessions: especially around auth, KYC, and payments
- Dependency governance: lockfile discipline, package review, and upgrade cadence
- Redaction rules: logs, analytics, crash reports, and support tooling
- Device trust decisions: what triggers step-up auth, what invalidates sessions
- Penetration testing preparation: not just the test itself, but fixes and retest time
Security maturity isn't a set of badges. It's the result of many boring, consistent engineering decisions.
The Path to Production CI/CD Testing and Release
Analysts at Kitrum found that slow performance, transaction failures, and weak connectivity drive a large share of mobile banking app abandonment. That tracks with what teams see in production. Users rarely separate a rendering delay from a payment problem. They read both as “my bank app is unreliable.”
Release quality for banking apps needs explicit gates before release week. Engineering, product, compliance, support, and fraud should agree on those gates early. If they do not, the first real definition of “done” shows up during an incident.
Test the journeys that carry identity and money
A useful test strategy is selective, not bloated. Fast checks belong in CI. Contract validation should catch backend drift, especially when a modern React frontend sits in front of legacy core banking services that still return inconsistent states, delayed confirmations, or fields that change by environment.
The test pyramid usually looks like this:
- Unit tests: reducers, hooks, formatters, validation rules, permission checks, and state transitions
- Integration tests: auth refresh, API contract parsing, transfer orchestration, KYC status mapping, and error normalization from upstream providers
- End-to-end tests: sign in, onboarding, account view, beneficiary setup, transfer submission, failed payment handling, and session recovery
For React Native, I would test device-specific behavior aggressively. App resume, biometric fallback, deep linking from email or SMS, and offline recovery fail in ways browser-based suites never see. For Next.js PWAs, the sharp edges are different. Redirect loops, cookie expiry, tab restore, cache invalidation, and service worker updates deserve heavier browser automation.
Coverage percentage is a weak release signal. Confidence on money movement and identity flows is the signal that matters.
CI/CD should remove surprises, not add automation theater
A banking delivery pipeline does not need to be clever. It needs to be repeatable, inspectable, and boring.
A practical release path for both React Native and Next.js usually includes:
- Linting, type checks, and schema validation
- Unit and integration test execution
- Security scanning and dependency review
- Environment-specific builds with locked configuration
- Automated deployment to staging
- Manual production approval with release notes and rollback steps
- Post-deploy smoke tests on critical flows
The trade-off between React Native and a Next.js PWA becomes obvious here. React Native gives better device integration and stronger control over biometrics and native secure storage, but release rollback is slower because app stores sit in the path. A Next.js PWA gives much faster rollback and simpler staged rollout, but browser storage rules, service worker behavior, and cross-browser auth differences create their own failure modes. Teams often underestimate that second category.
One common PWA failure is a stale service worker after an auth, consent, or API contract change. One common React Native failure is shipping the wrong environment config into a signed build and learning about it after store approval. Both are preventable. Neither is rare.
Performance work belongs in the release checklist
Performance issues in banking apps show up as trust issues. If balances render late or transfer confirmation hangs, support tickets rise and failed-transfer anxiety rises with them.
Release readiness should include:
- Code splitting for non-core modules
- Lazy loading for support, education, and secondary flows
- Bounded loading states instead of infinite spinners
- Explicit sync and retry logic for partial connectivity
- Real-user monitoring and alert thresholds after launch
Kitrum’s pre-launch mobile banking checklist also recommends concrete quality gates before release instead of vague “looks stable” sign-off, which is the right instinct for this category: Kitrum’s pre-launch mobile banking checklist.
Define thresholds before the first production push
Numeric gates force better conversations. They also expose disagreements early, especially where frontend behavior depends on slow or inconsistent responses from legacy banking cores.
Use thresholds such as:
- Crash rate limits for production-like test runs
- Transaction success targets for primary payment and transfer flows
- API error budgets for critical endpoints
- Latency limits for balance, transaction history, and transfer confirmation screens
- Recovery expectations for session expiry, provider timeout, and duplicate-submit protection
The exact numbers vary by product and regulator, but the pattern does not. If no one can state the release threshold for failed transfers, duplicate payments, or stuck KYC sessions, the team is not ready to ship.
A launch checklist that catches real production issues
Use a final gate that reads like an operations review.
| Release area | What to verify before launch |
|---|---|
| Auth | session expiry, biometric re-entry, device change handling, lockout recovery |
| KYC | retries, manual review states, partial progress resume, provider timeout behavior |
| Payments | idempotent retries, pending states, webhook reconciliation, reversal handling |
| Observability | dashboards, alert routing, redaction-safe logs, traceability for critical flows |
| Support readiness | internal runbooks, user-facing status messages, escalation path for failed transfers |
| Rollback plan | feature flags, safe disable paths, app version constraints, fallback messaging |
One detail teams miss in first releases is ownership of intermediate states. “Pending transfer,” “KYC under review,” and “payment submitted” need one shared definition across frontend, support, fraud, and operations. If each group interprets them differently, users get contradictory answers and incident triage slows down.
For teams setting up the delivery process from the ground up, this guide to making an app from scratch with React and Next.js is a useful reference for structuring milestones, environments, and release checks without overbuilding the pipeline.
The first production version does not need every planned feature. It needs stable flows, clear failure states, safe rollback paths, and enough telemetry to diagnose problems before users flood support.










Add Comment