You push a Next.js app to Vercel, watch the build go green, click the production URL, and feel done. The UI works. The API routes respond. The auth flow passes a quick test.
Then the central question shows up. What exactly did that deployment expose?
That question matters more now than it did even a year ago. In Gigamon’s 2025 survey, 55% of organizations experienced a security breach in the past 12 months, a 17% year-over-year increase, and 70% of security leaders identified the public cloud as the riskiest environment (Gigamon hybrid cloud security survey). For JavaScript teams, that risk lands directly in everyday work: API routes, server actions, edge functions, object storage, CI secrets, preview deployments, and npm packages.
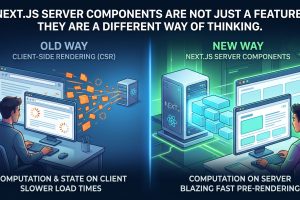
A lot of frontend developers still inherit an outdated mental model. They think security lives somewhere else, with the cloud provider, the platform team, or a future hire with “security” in their title. That model breaks in a modern React and Next.js stack. If your app fetches data on the server, writes to a database, calls third-party APIs, or runs code in serverless functions, you're already working on security-sensitive systems.
Introduction Why Cloud Security Matters for Your Next.js App
The moment a React team moves from static hosting to full-stack Next.js, the attack surface changes fast. A simple marketing site turns into a system with middleware, auth callbacks, API handlers, image optimizers, preview environments, background jobs, and cloud-managed storage. Vercel, Netlify, AWS, and Azure remove a lot of ops pain. They don't remove your security responsibilities.
That’s why “set it and forget it” is such a dangerous mindset in cloud projects. Managed platforms abstract servers, but they also make it easy to deploy risky defaults. A developer can add an API route, connect a bucket, paste a service key into environment variables, and ship before anyone asks whether access is scoped correctly, whether logs expose secrets, or whether a preview deployment leaks production data.
For Next.js teams, cloud computing security risks usually don't start with some cinematic breach. They start with ordinary decisions that feel harmless in the sprint. A permissive IAM role because a deploy was failing. A public asset bucket because image loading was blocked. A webhook endpoint with weak verification because the third-party docs were confusing. A package install during a rushed release because the feature had to go out that day.
Security work in JavaScript teams often looks like boring engineering discipline. That's exactly why teams skip it until production forces the issue.
A secure cloud app doesn't come from one big tool. It comes from dozens of small choices made well, repeatedly, by the same people writing the app.
Understanding the Cloud Security Battlefield
The cleanest way to understand cloud security is the apartment-building analogy. The cloud provider secures the building, the lobby, the elevators, and the external doors. You still have to lock your apartment, choose who gets keys, decide what stays visible from the window, and avoid taping your access code to the hallway wall.
That’s the shared responsibility model in practice. AWS, Azure, Vercel, and Netlify handle different layers of infrastructure and platform security. Your team still owns application logic, identity design, access control, API behavior, secrets handling, data exposure, and deployment hygiene. Teams that ignore that line usually end up surprised by breaches that were technically “their problem” all along.

If you're building full-stack React apps and want the broader architecture context, this guide on cloud-based application development for modern JavaScript teams helps frame where deployment and security responsibilities meet.
The risks most teams actually face
A lot of cloud security content stays too abstract to help developers. In practice, JavaScript teams usually run into a small set of recurring problems:
| Risk area | What it looks like in a React or Next.js stack | Why teams miss it |
|---|---|---|
| Misconfigurations | Public storage buckets, exposed preview environments, loose CORS rules, databases reachable more broadly than intended | Defaults feel convenient, and ownership is split across app and infra |
| IAM failures | Overpowered service accounts, serverless functions with broad permissions, stale credentials | Permissions get widened to unblock delivery and rarely get tightened later |
| Insecure APIs | Missing authorization checks, weak input validation, unprotected internal endpoints | Teams focus on frontend polish and assume auth equals authorization |
| Data leakage | Secrets in logs, user data in client bundles, cache leaks, server-rendered data crossing tenant boundaries | Data flows through many layers, so leaks hide in normal features |
| Supply-chain and CI/CD issues | Risky npm packages, leaked env vars, poisoned build steps, unreviewed GitHub Actions | Build systems feel operational, not security-critical |
| Multi-tenant platform risks | Shared environments, cross-environment confusion, accidental access from staging to production services | Managed platforms reduce friction, which also reduces friction for mistakes |
Where teams get the model wrong
The most common misunderstanding is simple: developers treat managed hosting like managed risk. It isn't.
A Next.js app on Vercel still needs disciplined auth boundaries, secret scoping, and careful server-side code. An SSR app on AWS still needs sane IAM design and storage controls. A static frontend that talks to third-party APIs still needs strict environment management and defensive client code.
Practical rule: If your code can read it, write it, trigger it, or deploy it, your team owns the security consequences of that path.
The battlefield isn't just “the cloud.” It's every join between code, config, identity, and automation.
Risk Deep Dive Infrastructure Gaps and Identity Failures
Most cloud incidents still come down to configuration mistakes and access problems. Check Point’s 2025 reporting says cloud misconfigurations are the leading cause of incidents, with 65% of organizations experiencing a cloud-related security event in the past year. It also notes that 29% of organizations still host “toxic cloud trilogies,” meaning publicly exposed, critically vulnerable, and highly privileged workloads (Check Point cloud security challenges 2025).
That sounds abstract until you map it to a real JavaScript stack.

Misconfiguration usually starts as convenience
A team exports static assets to object storage. The app needs fast public reads, so someone opens the bucket wider than necessary. Another developer provisions a managed database and keeps network access broad because local testing was painful. A preview deployment gets wired to production APIs because duplicating the data layer felt like overkill.
None of those decisions look dramatic at the time. Together, they create the exact pattern attackers want: exposed resources, weak boundaries, and easy lateral movement.
For Next.js teams, common infrastructure mistakes include:
- Public storage by accident. Static exports, uploaded images, backups, and generated reports end up accessible more broadly than intended.
- Environment crossover. Preview or staging deployments reuse production secrets, production queues, or production databases.
- Loose platform settings. Middleware, rewrites, webhooks, and internal routes stay reachable because nobody revisits initial defaults after launch.
- Drift between code and cloud. Terraform, Pulumi, dashboard changes, and manual fixes stop matching reality.
The practical problem isn't just exposure. It's uncertainty. Once settings drift, nobody knows which access rules are intentional and which ones are leftovers.
IAM is where prototypes become liabilities
Identity and Access Management tends to fail in the same predictable way. Teams start with broad permissions to move fast. Those permissions survive into production because tightening them feels risky, tedious, or easy to postpone.
That’s especially dangerous in serverless systems. A Next.js app may call cloud storage, queues, databases, analytics pipelines, email services, and background workers from one deployment. If the function or service account behind that app has blanket permissions, one compromised route can reach far beyond the feature that was attacked.
A few patterns show up constantly:
| Weak IAM pattern | Typical reason it happens | Better approach |
|---|---|---|
| One service account for many jobs | Faster setup | Separate roles by function and environment |
| Wildcard permissions | Hard to debug exact scopes | Grant the minimum actions needed for each resource |
| Long-lived credentials | Easy compatibility with older tooling | Prefer managed identity flows and rotate when static secrets are unavoidable |
| Shared admin access across team members | Startup speed | Individual accounts, role separation, and auditable access |
Least privilege isn't a theoretical best practice. It's what stops a small mistake in one route from becoming account-wide access.
What good teams do differently
Strong teams treat infrastructure and identity as application code, not as setup trivia. They review permission changes in pull requests. They separate staging from production with different secrets and roles. They make “temporary” access expire by default. They audit what a function can do, not just whether it works.
They also stop trusting green deployments as proof of safety. A successful deploy only proves the system runs. It says nothing about whether the data path is overexposed or whether the role behind that path can touch more than it should.
Use a simple review pass before every meaningful release:
- Check externally reachable resources. Buckets, webhooks, asset paths, preview URLs, dashboards, and API endpoints.
- Inspect function and service permissions. Ask what each role can read, write, delete, or invoke.
- Separate environments hard. Different secrets, different stores, different queues, different access.
- Remove dormant access. Old users, legacy tokens, unused integrations, abandoned build credentials.
A helpful explainer on the infrastructure side sits below. Watch it after you've looked at your own settings so the examples map to something concrete in your stack.
Risk Deep Dive Application Threats in a Serverless World
Infrastructure mistakes are only half the story. The other half lives in code paths your team writes every day: API routes, server actions, GraphQL resolvers, middleware, webhook handlers, and anything that turns a request into data access.
Within modern React stacks, many cloud computing security risks become visible to users.

Proofpoint describes insecure APIs as a top threat in multi-cloud setups, and the same material notes that 40% of serverless breaches stemmed from over-privileged IAM roles in event triggers (Proofpoint cloud security threat reference). That pairing matters because serverless apps often connect application bugs to oversized permissions.
A logged-in user is not an authorized user
One of the most common mistakes in Next.js is assuming auth automatically handles authorization. It doesn’t.
A user can be authenticated and still be allowed to fetch data they should never see. That’s how weak object-level checks happen. An API route receives a project ID, order ID, or user ID, queries the database, and returns data because the route verified the session but never confirmed ownership or role-based access to that specific resource.
This shows up in patterns like:
- Direct database fetches by arbitrary IDs in route handlers or server actions
- GraphQL resolvers that trust the client query shape more than server-side policy
- Admin-only operations gated by frontend UI instead of server-side checks
- Webhook endpoints that accept events without strict signature verification
If your team uses session libraries, keep the distinction clear. Authentication answers who the user is. Authorization answers what that user can do right now on this exact record. If you're refining that layer, this guide on NextAuth.js implementation patterns is a useful companion for the app side of identity work.
A secure API route doesn't ask only “is there a session?” It asks “does this identity have permission to perform this operation on this resource in this environment?”
Serverless changes how failures spread
Traditional servers are easier to reason about because teams tend to see them as infrastructure. Serverless functions feel smaller and less dangerous. That's misleading.
A Vercel Function or Lambda handler may execute with broad cloud permissions, receive untrusted input from webhooks or frontend requests, and call multiple internal services in a single invocation. If input validation is weak or event payloads are trusted too quickly, that function becomes a bridge between the public internet and privileged internal systems.
A few examples from real engineering practice:
| Threat pattern | What it looks like in Next.js | Better defense |
|---|---|---|
| Event-data injection | A webhook handler trusts incoming payload fields and triggers sensitive internal actions | Verify signatures, validate schemas, and restrict side effects |
| BOLA in API routes | /api/invoices?id=... returns records across tenants | Enforce record-level authorization server-side |
| Excessive data exposure | A route returns entire objects when the client only needs a subset | Shape responses deliberately and minimize fields |
| Unsafe SSR data use | Server-rendered pages pull sensitive data and cache or expose it incorrectly | Separate public from sensitive rendering paths and audit cache behavior |
What works in application-layer defense
The teams that do this well build friction into request handling on purpose. They use schema validation at the boundary. They centralize authorization policies. They reject unknown inputs early. They limit what each endpoint returns. They assume every request path will eventually be probed.
A reliable application security pattern for JavaScript teams looks like this:
- Validate input at the edge with libraries such as Zod or Valibot before business logic runs.
- Authorize every sensitive action at the route, resolver, or action layer. Never trust the client to enforce visibility.
- Constrain data returned so handlers send only the fields the UI needs.
- Treat webhooks as hostile until proven otherwise. Verify signatures, timestamps, and event intent.
- Log carefully. Record enough to investigate abuse without dumping tokens, full payloads, or user secrets into observability tools.
Application security is where frontend teams become real platform teams. Once you own server-side rendering and API logic, secure coding isn't adjacent to your work. It is the work.
Risk Deep Dive The Hidden Dangers in Your Dev Workflow
A lot of teams protect production and ignore the path that creates production. That’s a mistake. Your repo, build steps, dependencies, GitHub Actions, Vercel integration, and package-lock file are part of the attack surface.
The modern JavaScript ecosystem finds itself in an uncomfortable position. The same speed that makes npm and hosted CI/CD so productive also makes them attractive to attackers. A malicious package doesn't need to break your app to win. It only needs to reach your build agent, your environment variables, or your deployment token.
A practical guide to Next.js environment variables is worth revisiting here because secrets handling mistakes often begin in development, then get copied into preview and production workflows.
npm can act like a Trojan Horse
The package itself may look harmless. The danger can sit in install scripts, dependency chains, maintainer compromise, or typosquatted names that resemble a trusted library. JavaScript teams often evaluate packages for DX, bundle size, and stars. They rarely evaluate maintainer trust, install behavior, permission needs, and blast radius inside CI.
The workflow risk is simple. Once a package runs during install or build, it may access the same environment your trusted tooling can access. If that environment contains cloud keys, deployment tokens, signing secrets, or internal registry credentials, the compromise moves quickly.
W2S Solutions cites a CNCF survey showing 68% of organizations using containers face unpatched vulnerabilities due to ephemeral workloads, and it also cites reports showing 35% growth in supply-chain attacks on npm packages hosted in cloud registries (W2S discussion of cloud security risks). Even if your app isn't heavily containerized, the lesson applies to hosted build systems too. Temporary environments often hide persistent risk.
CI/CD pipelines leak in ordinary ways
Teams usually imagine pipeline attacks as highly specialized. In practice, many failures are mundane:
- Build logs print secrets because a debug statement dumped env vars or request headers.
- Preview deployments access production services because the same variables were reused everywhere.
- Third-party GitHub Actions get broad permissions with little review.
- Docker images or build tools are pulled on trust without verification or patch discipline.
- Deploy tokens stay valid too long and outlive the people or systems that first needed them.
Your pipeline isn't just a delivery tool. It's a privileged runtime with access to code, secrets, and production pathways.
The workflow habits that reduce risk
Not every team needs a heavy enterprise process. Most need better defaults and stricter review where it counts.
Use this workflow checklist as a baseline:
- Pin and review dependencies instead of accepting broad version drift in critical packages.
- Scan before merge using dependency auditing and code scanning in pull requests.
- Scope secrets by environment so preview, staging, and production don't share blast radius.
- Treat third-party actions as code. Review them, pin versions, and limit permissions.
- Keep builds minimal. If a job doesn't need production credentials, don't expose them to that job.
The hidden danger in dev workflow isn't that it looks insecure. It's that it looks routine.
An Actionable Security Playbook for JavaScript Teams
Development teams don't fail because they lack security advice. They fail because the advice doesn't fit how React and Next.js projects are built. What works is a repeatable playbook that lives inside code review, deployment, and team habits.
CrowdStrike highlights the skills problem here, noting 45% of organizations report insufficient cloud-native expertise, and it also cites a Gartner projection of a 25% rise in frontend-related breaches from unmanaged attack surfaces in micro-frontends (CrowdStrike overview of cloud security risks). For JavaScript teams, the answer isn't to become a full security department. It's to operationalize a smaller set of practices consistently.

Build guardrails before you need heroics
The strongest pattern is prevention by default. Don't rely on engineers remembering every rule under release pressure.
A practical baseline looks like this:
- Use infrastructure as code with Terraform, Pulumi, or cloud-native templates so access rules and resource settings are reviewable.
- Add policy checks in CI so dangerous changes fail before deployment.
- Create separate identities per app function instead of one broad service principal for everything.
- Enforce schema validation in route handlers and server actions.
- Limit data exposure by designing explicit response objects rather than returning raw ORM results.
Detection matters because prevention won't be perfect
Even disciplined teams miss things. Detection is what turns a mistake into a contained incident instead of a silent one.
For cloud and platform visibility, useful controls include:
| Control area | What to watch | Why it matters |
|---|---|---|
| Cloud posture | Public resources, permissive roles, config drift | Catches risky infra states before attackers do |
| Runtime monitoring | Unusual function behavior, spikes in access, strange invocation patterns | Helps identify abuse in serverless and edge environments |
| Repo and CI monitoring | Secret exposure, dependency anomalies, suspicious workflow changes | Protects the path to production |
| Application logs | Repeated authorization failures, enumeration attempts, webhook abuse | Reveals app-layer probing that infra tools may miss |
Good monitoring is selective. If alerts are noisy, teams ignore them. Start with events tied to privilege, exposure, identity change, and sensitive data paths.
The best alert is the one an engineer will act on within minutes because it clearly describes a meaningful change in risk.
A playbook teams can actually run
Use this as a standing checklist for React and Next.js projects.
Before coding starts
- Define trust boundaries. List what runs client-side, server-side, in edge functions, and in third-party services.
- Decide where secrets live. Keep them server-side and map which environments need which values.
- Choose the auth model early. Session shape, role model, and record-level authorization shouldn't be afterthoughts.
During implementation
- Validate every external input. Requests, webhooks, form bodies, query params, and third-party payloads.
- Keep authorization close to data access. Don't spread permission logic across UI components.
- Minimize privileged operations. If a function only reads one bucket path, don't let it manage the whole account.
- Review npm additions carefully. Especially packages with install scripts, low maintenance visibility, or deep transitive trees.
During CI and deployment
- Separate preview from production with different env vars and different backing services where possible.
- Restrict build permissions so jobs only get what they need.
- Scan dependencies and code changes automatically before release.
- Review infra diffs with the same seriousness as application code.
After release
- Audit public surfaces regularly. Routes, buckets, callbacks, asset paths, preview URLs, and dashboards.
- Rotate and prune credentials. Remove anything unused, stale, or too broad.
- Inspect logs for abuse patterns. Especially enumeration, repeated authorization failures, and webhook anomalies.
- Run incident drills. Know who revokes tokens, pauses deployments, rotates secrets, and checks audit logs.
Security for JavaScript teams works best when it's treated as an engineering system. Clear ownership, reviewable changes, strong defaults, and fast rollback beat vague “security awareness” every time.
Quick Answers on Cloud Security for Frontend Teams
Are Vercel or Netlify defaults enough for production apps
They're a helpful starting point, not a complete security model. Managed platforms reduce server management, but your team still owns auth rules, API protection, secret scoping, data access, and dependency hygiene.
What's the single highest-value task for a solo developer shipping an MVP
Review every place the app can touch real data or credentials. Tighten permissions, separate environments, and confirm no secret or admin action is reachable from client code or weak API routes.
How should teams manage secrets across environments
Keep secrets server-side, scope them by environment, and avoid reusing production values in previews or staging. Treat build logs, CI variables, and local .env files as sensitive assets, not convenience files.
What's the most common mistake in full-stack Next.js apps
Teams authenticate users, then forget to authorize access to specific resources. A valid session does not mean the user should see every record requested by an ID in the URL or body.
Do frontend developers really need to care about cloud computing security risks
Yes. In a modern Next.js stack, frontend developers often own route handlers, server actions, deployment settings, package choices, and runtime integrations. That's already security-critical work.
Next.js teams ship fastest when they pair velocity with strong engineering habits. Next.js & React.js Revolution publishes practical guides, deployment workflows, and deep dives that help React and Next.js developers build production-ready apps with fewer blind spots.











Add Comment